Demystifying Apache Kafka: The Internal Architecture Driving Massive Event Streaming by Nitin Goyal on April 20, 2026 232 views
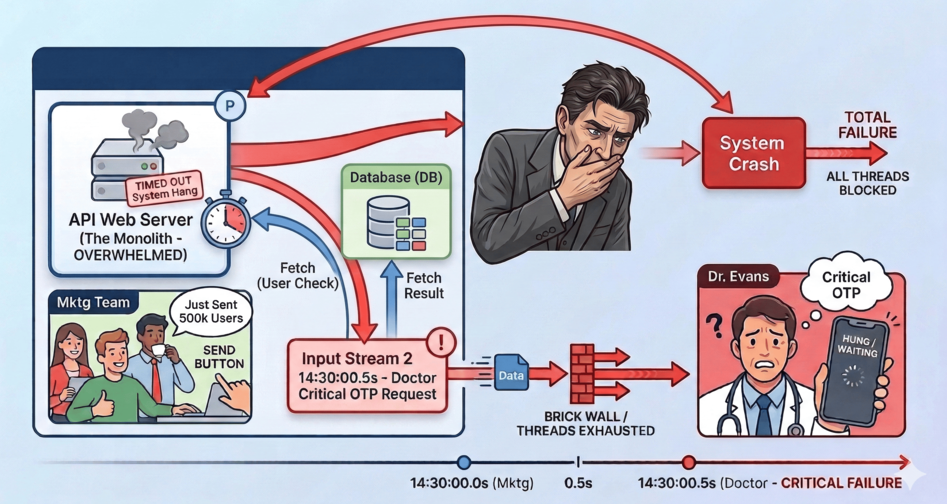
Imagine you’ve just built a thriving healthcare platform. Everything is humming along nicely until one fateful afternoon. A doctor requests a critical OTP to log into the portal. Exactly 0.5 seconds prior, your marketing team triumphantly clicked “Send” on a promotional SMS broadcast to 500,000 users. In your monolithic server, a thread loops over the 500,000 users in the database. Think about the sheer weight of that transaction for a moment: fetching thousands of users…
Anatomy of a Cookie Heist — Reverse Engineering an Info-Stealer by Pratik Dabhi on April 8, 2026 134 views

What looked like a simple setup.exe turned out to be a stealthy info-stealer that stole Microsoft 365 session tokens from Chrome cookies — completely bypassing MFA. Here’s the full forensic breakdown. Introduction Suspicious login activity was observed from multiple geographic regions, inconsistent with known user behavior. Earlier this month, our team investigated a real-world malware incident involving the theft of Microsoft 365 session tokens via Chrome cookies. What initially appeared to be a harmless setup…
From Developer to Architect -Episode1 by Shifa Salheen on March 10, 2026 201 views
Everything Worked, Until Traffic Arrived Ever heard terms like Horizontal scaling and Vertical scaling? They appear everywhere in architecture diagrams, in interviews, in system design conversations. At first, they sound like infrastructure jargon. Abstract. Distant. Something you’ll “learn later.” But they aren’t. They’re part of a transition every developer eventually goes through often without realizing it. From Writing Code to Designing Systems You start as a developer. You write code. You focus on features. You…
How Machines Hear: The Magic of Audio Fingerprinting by Anjan Sampath on January 27, 2026 344 views

You’re sitting in a cafe, chilling ☕ — where the drinks are overpriced and the atmosphere is a mix of music, chatter and one guy whose laugh sounds like an engine starting. 🚗 Suddenly, a song starts playing and you know you’ve heard it before. But from where? So you pull out your phone and open Google. Tap “Search a song” 🎶 Hold it up. 🤳 Two seconds later - boom! It knows the song.…
Threads in Java: From Kitchen to Code by Tarunkumar Mulchandani on January 5, 2026 310 views
In our previous post(Multitasking in kitchen), we explored the basics of threading through the lens of mom’s multitasking how she prepares breakfast by juggling multiple tasks efficiently. In this post, we’ll shift our focus to actual Java programming constructs for creating threads. We’ll also continue to relate it back to mom’s kitchen, because her routine still makes for a surprisingly accurate analogy. Preparing Tiffin as a Process Let’s say the overall job is to prepare…
💰The Memory Vault: Where Your Code Keeps Its Variables by Sufyan Gazdhar on December 22, 2025 336 views
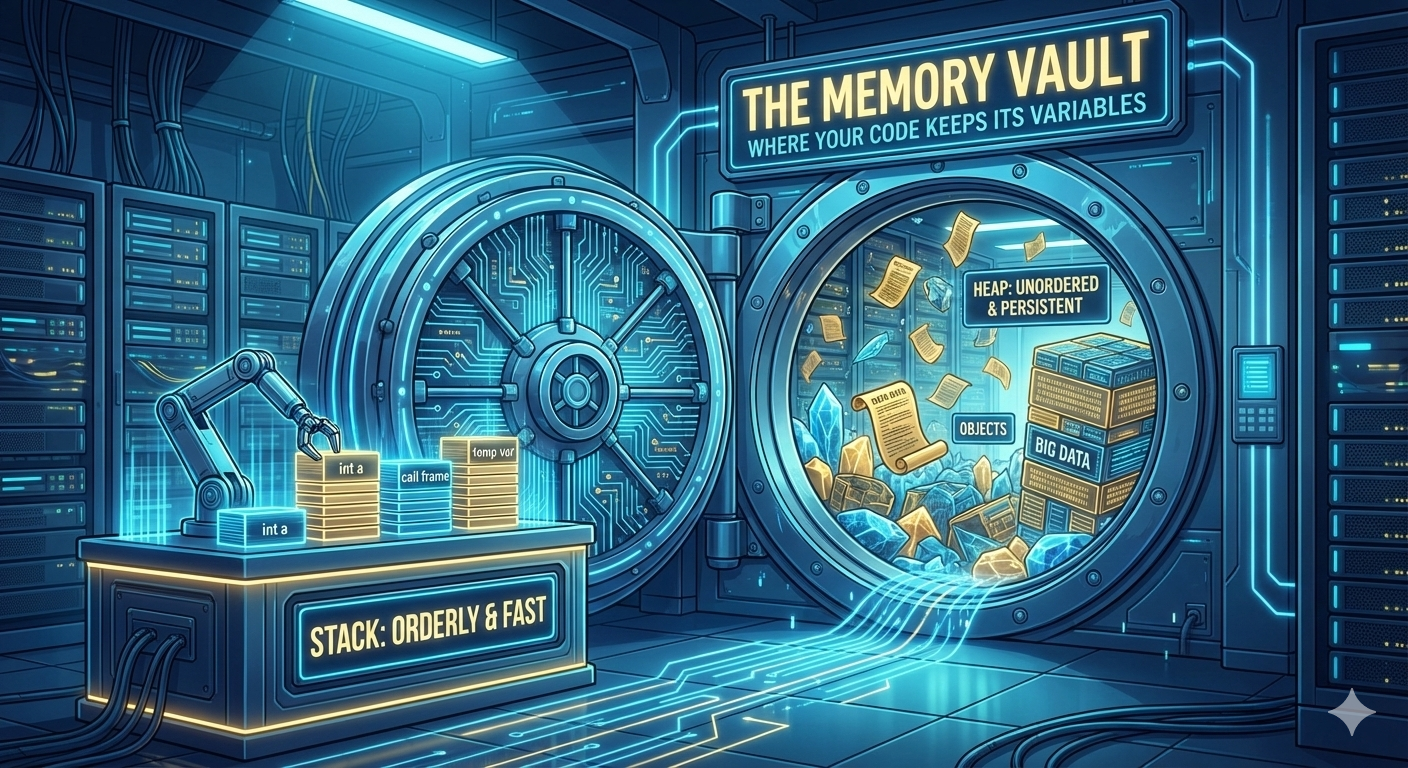
When your code runs, it’s constantly stashing, retrieving, and discarding data, variables that define how your logic behaves. But where does all of this information actually go? Under the hood, your computer has a system, fast, organized, and surprisingly elegant, for deciding where each variable lives, how long it stays there, and how it’s accessed. In this deep dive, we’ll unlock The Memory Vault, revealing how your code uses two powerful storage zones - the…
Debugging Nightmares: Episode 3 -Why Auditors Hate Your Superadmin by Shifa Salheen on November 27, 2025 537 views
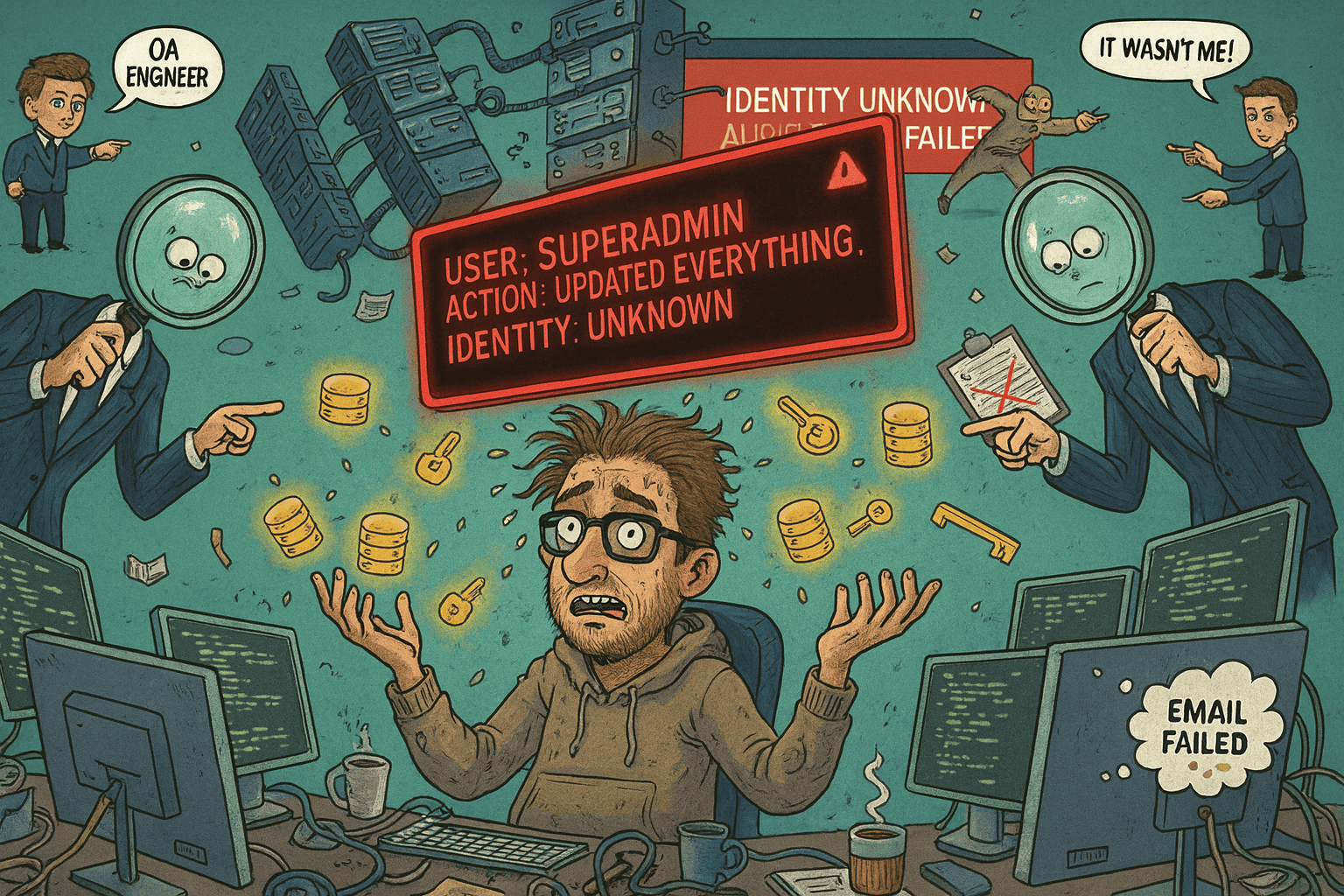
The Superadmin: Our Industry’s Favorite Shortcut Everyone has their own guilty pleasures.People think developers are addicted to coffee.Cute theory, but coffee never gave us Unlimited Power Mode. Our real addiction, our true obsession, is the Superadmin. Sure, coffee wakes us up…But Superadmin? Superadmin awakens the demon in us. It’s the “touch anything you want, break everything you shouldn’t” account.Irresistible. Illegal. Deliciously dangerous. Every project begins with the same sacred ritual:One insert query in Liquibase or…
Dear Code, you had One Job! by Hardik Kardam on October 31, 2025 568 views

Hey everyone! Ever been super proud of a chunk of code you wrote, only to have it blow up in your face later? 🤦♂️ That's exactly what happened to me recently. I was building a task manager for a surgery module. It was a pretty complex system with all sorts of entities: surgery_master, TaskMapping, surgery_booking, task_master, and a full-blown Task entity. My code was split into a couple of services and data classes, and I…
The Kitchen Concurrency: Multitasking with Threads by Tarunkumar Mulchandani on October 14, 2025 576 views

Every morning, our mom becomes a silent multitasking magician. She’s making tea, loading the washing machine, chopping vegetables, and waking everyone up almost at the same time. You watch in awe, wondering how it’s even possible. With just two hands, she keeps the entire household moving like a well-coordinated system. Here’s the secret: she’s not actually doing everything at once, but rather switching smartly between tasks. While the tea boils, she folds clothes. When the…
TLS is a Handshake, mTLS is a Hug. With zero Trust — no room for Thug. by Sahil Khan on September 29, 2025 616 views

In today’s distributed systems — especially microservices architectures — securing internal service-to-service communication is just as critical as securing public-facing APIs. This blog will walk you through what mTLS is, why it’s needed, and how to implement it with simple step-by-step commands and Spring Boot examples. 💡 Why Secure Inter-Service Communication? We are deploying a new user-service in production. It talks to auth-service, payment-service, and more. These services might be running: On different machinesInside containers…