Debugging Nightmares: Episode 3 -Why Auditors Hate Your Superadmin by Shifa Salheen on November 27, 2025 458 views
The Superadmin: Our Industry’s Favorite Shortcut
Everyone has their own guilty pleasures.
People think developers are addicted to coffee.
Cute theory, but coffee never gave us Unlimited Power Mode.
Our real addiction, our true obsession, is the Superadmin.
Sure, coffee wakes us up…
But Superadmin? Superadmin awakens the demon in us.
It’s the “touch anything you want, break everything you shouldn’t” account.
Irresistible. Illegal. Deliciously dangerous.
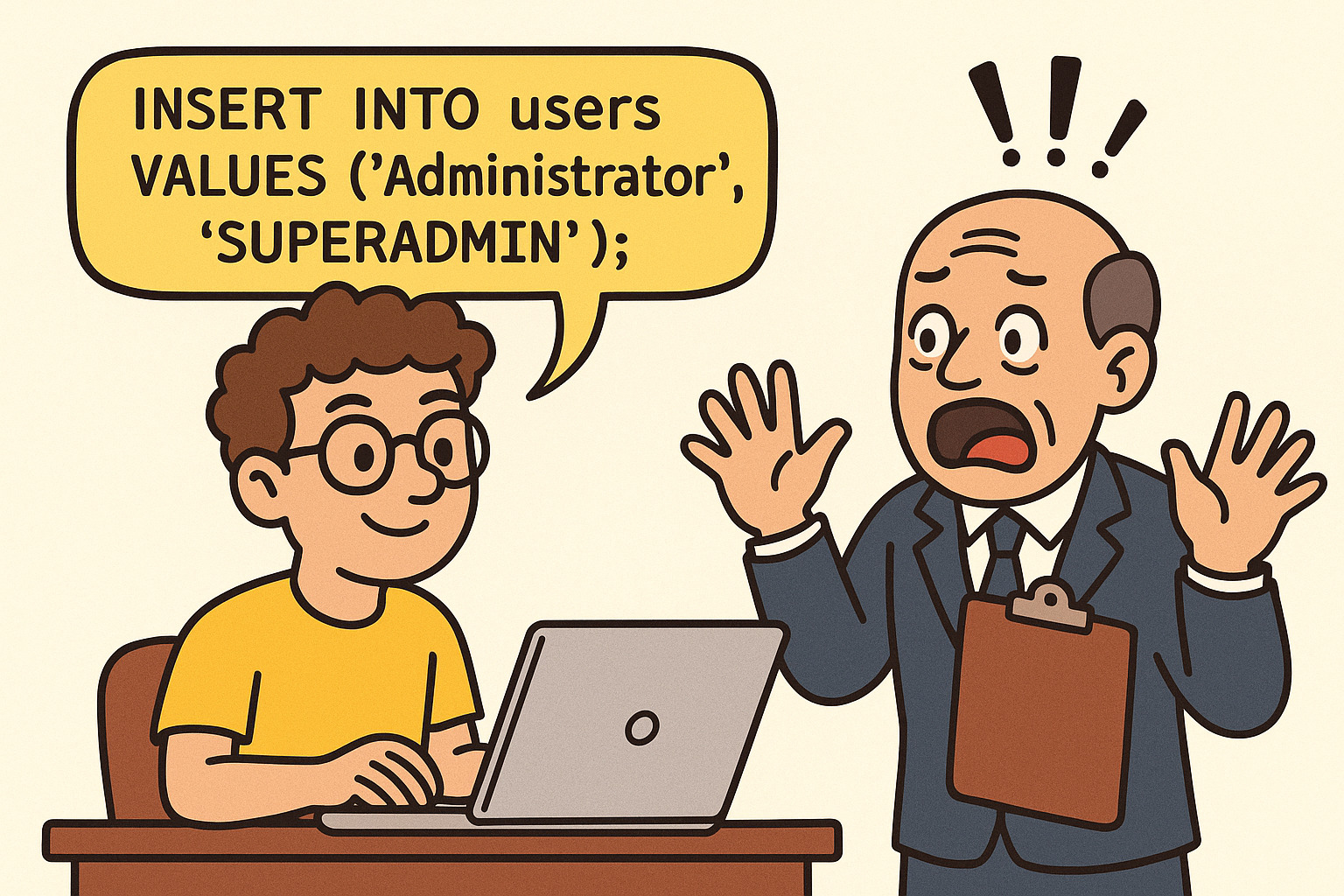
Every project begins with the same sacred ritual:
One insert query in Liquibase or Flyway that creates the GOD of all accounts.
INSERT INTO users (id, username, password, role) VALUES (1, 'Administrator', 'hashed-password', 'SUPERADMIN');
From that moment on, life feels easy
- QA logs in with Superadmin.
- Developers debug with Superadmin.
- DevOps checks configs with Superadmin.
- Delivery managers roam around with Superadmin.
Because Superadmin has access to everything, and let’s be honest, everyone wants full access.
One login to rule them all. One account to shortcut everything.
And also, one huge nightmare waiting to happen.
When “Administrator” Shows Up in Every Log
It all started on an ordinary Tuesday, the kind where nothing dramatic is supposed to happen.
On one of our staging servers, we had been using the Administrator account for everything.
Quick fixes, tests, configs, deployments, you name it, the Administrator did it.
And then, out of nowhere, the emails stopped working.
At first, we thought it was a tiny glitch.
Then we dug deeper… and found that someone had changed the email configuration.
Naturally, the question came up: “Who changed this?”
- QA swore it wasn’t them.
- Developers denied it.
- DevOps shrugged.
- The delivery manager insisted on innocence.
We opened the logs, hoping for clarity. Instead, we found:
User: Administrator Action: Updated Email Settings
That was it. Administrator. The all-knowing, all-access, all-blaming blackhole.
The result? QA was blocked, developers couldn’t verify their fixes, and the entire team slipped into a blame game as the whole Sprint revolved around 25 different kinds of Email Alerts, and everyone’s tasks went on hold for a while.
In that moment, our all-powerful Superadmin account wasn’t a blessing; it was a curse.
Why Everyone Creates Superadmin in the Beginning
If we’re honest, the pattern makes perfect sense in MVPs:
- Speed: No role-based blockers.
- Simplicity: One account, full access.
- Trust: Small team, high confidence.
It feels harmless.
It feels efficient.
And in a small team, it works… until it doesn’t.
Because that shortcut hides a trap.
The golden rule of compliance is brutally simple:
You must always be able to prove who did what, when, and why.
And the moment everyone uses superadmin, that rule shatters.
Least Privilege: The Principle Auditors Live By
The first thing auditors check isn’t your code, it’s your access model.
And the golden principle they enforce is Least Privilege.
What is Least Privilege?
Each user should have the minimum level of access required to perform their job and nothing more.
Why it matters:
- Limits damage: QA can’t accidentally destroy production data.
- Prevents abuse: no one person holds unchecked power.
- Creates accountability: actions are tied to real identities.
Least Privilege isn’t exciting to developers. But to auditors, it’s sacred.
Break it, and every framework, SOC2, ISO 27001, HIPAA, SOX, GDPR, will flag you.
How the Superadmin Shortcut Creeps Into Pipelines
And here’s the fun part: the “One Superadmin account” problem never stays small.
It starts as a local shortcut… and quietly sneaks into your CI/CD pipelines.
Most teams end up baking it straight into their Jenkins or GitHub Actions scripts:
pipeline {
stages {
stage('DB Migration') {
steps {
sh 'liquibase update'
sh '''
psql -d mydb -c "INSERT INTO users (username, role)
VALUES ('Administrator', 'SUPERADMIN');"
'''
}
}
}
}
Now every environment, dev, staging, sometimes even prod, has the same all-powerful account.
And when auditors read your Jenkinsfile, they don’t see “efficiency.”
They see evidence of systemic bad practice.
The Compliance Nightmare
The day auditors walk in, your “God account” shortcut becomes your biggest liability
Superadmin: the blackhole of accountability.
Superadmin feels great… until you realize how many rules, logs, and approvals it silently destroys. Let’s count the casualties.
1. Least Privilege Violation
“Why does every user have full rights?”
SOC2 requires clear role separation.
2. Audit Trail Failure
Logs showing only “Administrator” provide no accountability.
3. Change Management Gaps
Shared superadmin = no link between changes and approvals.
4. Credential Management Risks
Shared passwords in Slack/Notion = instant red flag.
The account that made life easy can cost you months of compliance fixes and enterprise deals.
MVP Shortcuts vs Compliance Reality
The moment you compare MVP shortcuts with actual compliance requirements, the illusion of God account disappears fast.
MVP Shortcuts
- Seed one superadmin role, and everyone is unblocked instantly.
- Share the same login — QA, devs, managers all play God.
- Jenkinsfile seeds superadmin everywhere — every environment is identical.
- Logs just say Administrator — quick setup, zero friction.
But the day auditors walk in, you’ll wish you had built it differently
Compliance Reality
- Seed multiple roles from day one (QA, Dev, Viewer, Admin).
- Give per-user logins so actions are traceable.
- Pipelines should seed role-based accounts, not global Gods.
- Logs must capture real identities. Alice updated the config, not “Administrator.”
The Refactor Path: From God Mode to Guardrails
If Superadmin got you into trouble, this is how you get out, without breaking the system or your audit report.
- Seed Roles From Day One
A system collapses when everyone acts as “Administrator.” Define real roles early so access naturally separates as the team grows.
INSERT INTO roles (id, role_name) VALUES (1, 'SUPERADMIN'), (2, 'DEVELOPER'), (3, 'QA'), (4, 'VIEWER');
QA uses QA role, devs use DEV, and only a select few hold SUPERADMIN.
This single step prevents 80% of your compliance headaches.
2. Per-User Accounts
- Avoid shared logins even in development.
When every action maps to an actual person, mistakes become visible and fixable, not a guessing game. - Example:
qa_user,dev_user,admin_user
3. Immutable Logs
- Logs should record who did what, not “Administrator did everything.”
This is where auditors look first, and it’s where most teams fail.
User: alice.qa Action: Updated Email Configuration
A clean identity trail is more valuable than any technical optimization you do.
4. SSO + RBAC
Integrate identity early — Okta, Auth0, Cognito, Keycloak, anything.
Centralized RBAC ensures people get only the permissions they need.
And most importantly:
Never let Jenkins auto-create a universal Superadmin across environments.
A convenient pipeline today becomes a compliance crime scene tomorrow.
Conclusion: When Convenience Becomes Chaos
The first migration may feel like a harmless shortcut, but shortcuts don’t survive audits.
A superadmin isn’t a power; it’s a liability.
Because the nightmare isn’t just code breaking.
It’s the silence in your logs when you can’t prove who did what, when, or why.
That’s when the real debugging begins, not of software, but of trust.
So the next time you reach for that “Administrator” insert in your first migration, pause.
Ask yourself:
Do I want speed today, or compliance tomorrow?
Because one line of SQL can decide whether your project passes audits or collapses in the blame game.